Entries Tagged "cryptography"
Page 50 of 55
Power Analysis of RFID Tags
This is great work by Yossi Oren and Adi Shamir:
Abstract (Summary)
We show the first power analysis attack on passive RFID tags. Compared to standard power analysis attacks, this attack is unique in that it requires no physical contact with the device under attack. While the specific attack described here requires the attacker to actually transmit data to the tag under attack, the power analysis part itself requires only a receive antenna. This means that a variant of this attack can be devised such that the attacker is completely passive while it is acquiring the data, making the attack very hard to detect. As a proof of concept, we describe a password extraction attack on Class 1 Generation 1 EPC tags operating in the UHF frequency range. The attack presented below lets an adversary discover the kill password of such a tag and, then, disable it. The attack can be readily adapted to finding the access and kill passwords of Gen 2 tags. The main significance of our attack is in its implications any cryptographic functionality built into tags needs to be designed to be resistant to power analysis, and achieving this resistance is an undertaking which has an effect both on the price and on the read range of tags.
My guess of the industry’s response: downplay the results and pretend it’s not a problem.
Huge Vulnerability in GPG
GPG is an open-source version of the PGP e-mail encryption protocol. Recently, a very serious vulnerability was discovered in the software: given a signed e-mail message, you can modify the message—specifically, you can prepend or append arbitrary data—without disturbing the signature verification.
It appears this bug has existed for years without anybody finding it.
Moral: Open source does not necessarily mean “fewer bugs.” I wrote about this back in 1999.
UPDATED TO ADD (3/13): This bug is fixed in Version 1.4.2.2. Users should upgrade immediately.
Distributed Enigma Cryptanalysis
And you can help:
The M4 Project is an effort to break 3 original Enigma messages with the help of distributed computing. The signals were intercepted in the North Atlantic in 1942 and are believed to be unbroken.
EDITED TO ADD (3/8): One message has been broken.
More on Kish's Classical Security Scheme
Here’s an interesting rebuttal of Laszlo Kish’s theoretically secure classical communications scheme.
EDITED TO ADD (2/18): Kish’s response.
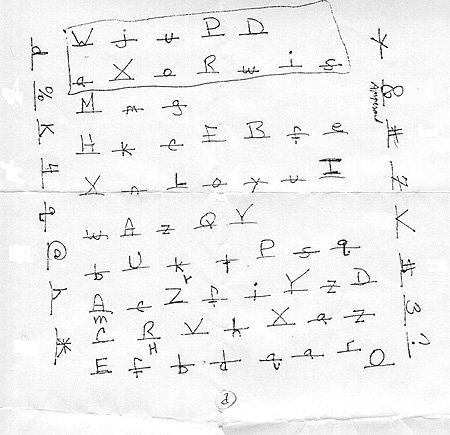
Handwritten Real-World Cryptogram
I get e-mail, occasionally weird e-mail. Every once in a while I get an e-mail like this:
I know this is going to sound like a plot from a movie. It isn’t. A very good friend of mine Linda Rayburn and her son Michael Berry were brutally murdered by her husband…the son’s stepfather.
They were murdered on February 3rd, 2004. He then hung himself in the basement of their house. He left behind a number of disturbing items.
However, the most intriguing is a cryptogram handwritten on paper utilizing letters, numbers and symbols from a computer keyboard. Linda’s daughter Jenn was the one who found the bodies. Jenn is a very good friend of mine and I told her I would do everything within my power to see if this cryptogram is truly a cryptogram with valuable information or if it is a wild goose chase to keep us occupied and wondering forever what it means.
I have no idea if any of this is true, but here’s a news blip from 2004:
Feb. 2: Linda Rayburn, 44, and Michael Berry, 23, of Saugus, both killed at home. According to police, Rayburn’s husband, David Rayburn, killed his wife and stepson with a hammer. Their bodies were found in adjacent bedrooms. David Rayburn left a suicide note, went to the basement, and hanged himself.
And here is the cryptogram:
The rectangle drawn over the top two lines was not done by the murderer. It was done by a family member afterwards.
Assuming this is all real, it’s a real-world puzzle with no solution. No one knows what the message is, or even if there is a message.
If anyone figures it out, please let me know.
The Doghouse: Super Cipher P2P Messenger
Super Cipher P2P Messenger uses “unbreakable Infinity bit Triple Layer Socket Encryption for completely secure communication.”
Wow. That sure sounds secure.
EDITED TO ADD (2/15): More humor from their website:
Combining today’s most advanced encryption techniques, and expanding on them. The maximum encryption cipher size is Infinity! Which means each bit of your file or message is encrypted uniquely, with no repetition. You define a short key in the program, this key is used in an algorithm to generate the Random Infinity bit Triple Cipher. Every time you send a message or file, even if it is exactly the same, the Triple Cipher completely changes; hence then name ‘Random’. Using this method a hackers chances of decoding your messages or file is one to infinity. In fact, I challenge anyone in the world to try and break a single encrypted message; because it can’t be done. Brute Force and pattern searching will never work. The Encryption method Super Cipher P2P Messenger uses is unbreakable.
43rd Mersenne Prime Found
Last month, researchers found the 43rd Mersenne Prime: 230,402,457-1. It’s 9,152,052 decimal digits long.
This is a great use of massively parallel computing:
The 700 campus computers are part of an international grid called PrimeNet, consisting of 70,000 networked computers in virtually every time zone of the world. PrimeNet organizes the parallel number crunching to create a virtual supercomputer running 24×7 at 18 trillion calculations per second, or ‘teraflops.’ This greatly accelerates the search. This prime, found in just 10 months, would have taken 4,500 years on a single PC.
Miller on OpenSSH
Interesting interview:
Federico Biancuzzi interviews OpenSSH developer Damien Miller to discuss features included in the upcoming version 4.3, public key crypto protocols details, timing based attacks and anti-worm measures.
Totally Secure Classical Communications?
My eighth Wired column:
How would you feel if you invested millions of dollars in quantum cryptography, and then learned that you could do the same thing with a few 25-cent Radio Shack components?
I’m exaggerating a little here, but if a new idea out of Texas A&M University turns out to be secure, we’ve come close.
Earlier this month, Laszlo Kish proposed securing a communications link, like a phone or computer line, with a pair of resistors. By adding electronic noise, or using the natural thermal noise of the resistors—called “Johnson noise”—Kish can prevent eavesdroppers from listening in.
In the blue-sky field of quantum cryptography, the strange physics of the subatomic world are harnessed to create a secure, unbreakable communications channel between two points. Kish’s research is intriguing, in part, because it uses the simpler properties of classic physics—the stuff you learned in high school—to achieve the same results.
At least, that’s the theory.
I go on to describe how the system works, and then discuss the security:
There hasn’t been enough analysis. I certainly don’t know enough electrical engineering to know whether there is any clever way to eavesdrop on Kish’s scheme. And I’m sure Kish doesn’t know enough security to know that, either. The physics and stochastic mathematics look good, but all sorts of security problems crop up when you try to actually build and operate something like this.
It’s definitely an idea worth exploring, and it’ll take people with expertise in both security and electrical engineering to fully vet the system.
There are practical problems with the system, though. The bandwidth the system can handle appears very limited. The paper gives the bandwidth-distance product as 2 x 106 meter-Hz. This means that over a 1-kilometer link, you can only send at 2,000 bps. A dialup modem from 1985 is faster. Even with a fat 500-pair cable you’re still limited to 1 million bps over 1 kilometer.
And multi-wire cables have their own problems; there are all sorts of cable-capacitance and cross-talk issues with that sort of link. Phone companies really hate those high-density cables, because of how long it takes to terminate or splice them.
Even more basic: It’s vulnerable to man-in-the-middle attacks. Someone who can intercept and modify messages in transit can break the security. This means you need an authenticated channel to make it work—a link that guarantees you’re talking to the person you think you’re talking to. How often in the real world do we have a wire that is authenticated but not confidential? Not very often.
Generally, if you can eavesdrop you can also mount active attacks. But this scheme only defends against passive eavesdropping.
For those keeping score, that’s four practical problems: It’s only link encryption and not end-to-end, it’s bandwidth-limited (but may be enough for key exchange), it works best for short ranges and it requires authentication to make it work. I can envision some specialized circumstances where this might be useful, but they’re few and far between.
But quantum key distributions have the same problems. Basically, if Kish’s scheme is secure, it’s superior to quantum communications in every respect: price, maintenance, speed, vibration, thermal resistance and so on.
Both this and the quantum solution share another problem, however; they’re solutions looking for a problem. In the realm of security, encryption is the one thing we already do pretty well. Focusing on encryption is like sticking a tall stake in the ground and hoping the enemy runs right into it, instead of building a wide wall.
Arguing about whether this kind of thing is more secure than AES—the United States’ national encryption standard—is like arguing about whether the stake should be a mile tall or a mile and a half tall. However tall it is, the enemy is going to go around the stake.
Software security, network security, operating system security, user interface—these are the hard security problems. Replacing AES with this kind of thing won’t make anything more secure, because all the other parts of the security system are so much worse.
This is not to belittle the research. I think information-theoretic security is important, regardless of practicality. And I’m thrilled that an easy-to-build classical system can work as well as a sexy, media-hyped quantum cryptosystem. But don’t throw away your crypto software yet.
Here’s the press release, here’s the paper, and here’s the Slashdot thread.
EDITED TO ADD (1/31): Here’s an interesting rebuttal.
Sidebar photo of Bruce Schneier by Joe MacInnis.