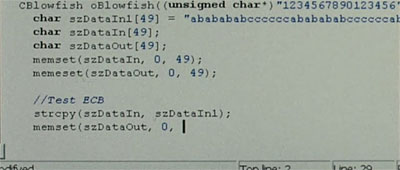
PowerLocker uses Blowfish
There’s a new piece of ransomware out there, PowerLocker (also called PrisonLocker), that uses Blowfish:
PowerLocker could prove an even more potent threat because it would be sold in underground forums as a DIY malware kit to anyone who can afford the $100 for a license, Friday’s post warned. CryptoLocker, by contrast, was custom built for use by a single crime gang. What’s more, PowerLocker might also offer several advanced features, including the ability to disable the task manager, registry editor, and other administration functions built into the Windows operating system. Screen shots and online discussions also indicate the newer malware may contain protections that prevent it from being reverse engineered when run on virtual machines.
PowerLocker encrypts files using keys based on the Blowfish algorithm. Each key is then encrypted to a file that can only be unlocked by a 2048-bit private RSA key. The Malware Must Die researchers said they had been monitoring the discussions for the past few months. The possibility of a new crypto-based ransomware threat comes as developers continue to make improvements to the older CryptoLocker title. Late last month, for instance, researchers at antivirus provider Trend Micro said newer versions gave the CryptoLocker self-replicating abilities that allowed it to spread through USB thumb drives.