September 2018
W. W. Norton & Company
288 Pages
ISBN: 978-0393608885
Ordering
Hardcover:
Amazon | Amazon.co.uk | Barnes & Noble | Bookshop.org
Paperback:
Amazon | Amazon.co.uk | Barnes & Noble | Bookshop.org
Ebook:
Amazon | Amazon.co.uk | Apple Books | Barnes & Noble
Order signed copies:
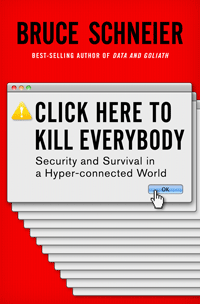
Click Here to Kill Everybody
Security and Survival in a Hyper-connected World
A Book by Bruce Schneier
The internet is powerful, but it is not safe. As “smart” devices proliferate the risks will get worse, unless we act now.
From driverless cars to smart thermostats, from autonomous stock-trading systems to drones equipped with their own behavioral algorithms, the internet now has direct effects on the physical world. While this computerized future, often called the Internet of Things, carries enormous potential, best-selling author Bruce Schneier argues that catastrophe awaits in its new vulnerabilities and dangers. Forget data theft: cutting-edge digital attackers can now literally crash your car, pacemaker, and home security system, as well as everyone else’s. In Click Here to Kill Everybody, Schneier explores the risks and security implications of our new, hyper-connected era, and lays out common-sense policies that will allow us to enjoy the benefits of this omnipotent age without falling prey to the consequences of its insecurity. From principles for a more resilient Internet of Things to a recipe for sane government oversight, Schneier’s vision is required reading for anyone invested in human flourishing.
Praise for Click Here to Kill Everybody
“Schneier skillfully guides readers through serious attacks that have happened already—and moves on to those he believes are just over the horizon […] Schneier sets out detailed solutions that should be required reading for politicians across the world.”
—Financial Times
“Schneier, more than the average policymaker or marketing blowhard, has a pretty good idea of what the actual benefits of these systems can be. He avoids the twin temptations of wholesale dismissal and breathless hype, and charts a course that manages the tricky business of being both nuanced and exciting.”
—Cory Doctorow, BoingBoing.net
“[Click Here to Kill Everybody] is sober, lucid and often wise in diagnosing how the security challenges posed by the expanding Internet came about, and in proposing what should (but probably won’t) be done about them.”
—Nature
“This thought-provoking book will mainly have you nodding in agreement and shaking your head in frustration. The future is not yet written, and so prediction, like attribution, is hard. Hopefully, enough people will read the book to change the path of the future. I plan to re-read it, and there can be no greater praise.”
—Paul Baccas, Virus Bulletin
“Useful for an internet user but particularly for those concerned with privacy, civil liberties, and related issues.”
—Kirkus Reviews
Table of Contents
Endnotes
High-Resolution Book Cover
Book Talk
Reviews
Boing Boing
Catholic Herald
CSO (Roger Grimes)
CSO (J.M. Porup)
Hidde de Vries
Financial Times
GovFresh
Harris Online
Kirkus
Library Journal
Make IT Work Blog
Nature
Nixu Blog
Open Letters Review
Palo Alto Networks Blog
Politico
Publisher’s Weekly
RSA Conference Blog
Scott Schober
Security Management
Virus Bulletin
ZDNet UK
Related Articles
Video Interviews
The Aspen Institute
Berkman Klein Center
Conversation with Nobel Minds
Fordham Law
Pacific Standard
Podcast and Radio Interviews
The 1A (NPR)
Berkman Klein Center
CBC Radio
The Cyberlaw Podcast
The Cyberwire
The Disruptors
The Lawfare Podcast
Le Show (Harry Shearer)
The NULLCON Podcast
Recode Decode
The Security Ledger
Social Media & Politics
Steal This Show
WNYC Radio
Written Interviews
up to Books
Sidebar photo of Bruce Schneier by Joe MacInnis.
